Every successful case you send to the lab contains more than models, scans, and photos—it carries protected health information (PHI) that must be safeguarded at every step. As digital dentistry accelerates, HIPAA compliant file sharing isn’t just “nice to have”; it’s table stakes for protecting patient privacy, avoiding costly breaches, and maintaining a smooth, professional relationship with your lab. For practices that regularly transmit photos, STL/PLY files, CBCT data, and Rx details, understanding HIPAA compliant file sharing dental workflows is the key to speed and security.
Associated Dental Lab has supported digital and analog workflows for decades, offering streamlined case intake, digital file handling, and strict quality controls “Made in the USA”—so you can focus on clinical outcomes while your lab protects the data behind the smile.
This guide explains how to choose the right channels (secure portals vs. email), set up multi-factor authentication portals, maintain HIPAA audit logs, and document HIPAA BAA (Business Associate Agreement) requirements where appropriate. You’ll get checklists, case examples, and plain-language rules you can adopt today—without slowing down production.
HIPAA Basics for File Sharing in Dentistry
What HIPAA requires (in a nutshell)
HIPAA’s Security Rule sets national standards for protecting ePHI with administrative, physical, and technical safeguards. In practice, that means risk-based controls such as access management, audit controls, transmission security, and workforce policies that keep PHI confidential, accurate, and available. HHS.gov
Encryption matters. HHS guidance treats encryption as an “addressable” safeguard under the Security Rule, but modern best practice strongly favors encryption in transit (e.g., TLS) and at rest (e.g., AES-256) for any system that stores or transmits ePHI.
Auditability matters. HIPAA requires the capability to record and examine system activity (audit controls). OCR’s audit program evaluates policies, controls, and documentation—so your file-sharing workflow should create traceable, retrievable records of who accessed what, when, and how.
MFA is the new normal. HHS has proposed updates to require multi-factor authentication (with limited exceptions), reinforce encryption, and strengthen cyber hygiene. Even before final rules, OCR already recommends MFA as a best practice to protect ePHI.
Do you need a BAA with your lab?
Here’s a nuance many teams miss: according to the American Dental Association, dental laboratories are health care providers. When you share PHI with a lab for treatment, a BAA may not be required for that sharing. However, if you use a third-party platform (e.g., cloud portal, email vendor, file-transfer service) to transmit or store PHI on your behalf, you do need a BAA with that vendor because they are your business associate under HIPAA.
Core Principles of HIPAA Compliant File Sharing Dental Workflows
1) Minimum necessary + clear purpose
Send only the elements your lab needs (name/ID, tooth numbers, scan, shade, photos). Avoid extra demographic data, insurance screenshots, or unrelated clinical notes.
2) Encrypt in transit and at rest
Use a secure file transfer healthcare channel that enforces TLS 1.2+ during transmission and AES-grade encryption at rest. If you must email, use HIPAA compliant email with automatic encryption and message-level protections.
3) Strong identity + multi-factor authentication portal
Require MFA for any system that houses or exchanges PHI with the lab. It’s increasingly an explicit regulatory expectation and already a published best practice.
4) Compliant HIPAA audit logs
Your platform should log access, downloads, edits, shares, IPs/locations, and admin changes. While HIPAA does not prescribe a single log format, retaining logs and related documentation for at least six years is a broadly adopted standard—consistent with HIPAA documentation retention timelines.
5) Proper agreements (BAAs)
Have a current HIPAA BAA with any non-provider vendor that stores or transmits ePHI for you (email provider, portal, SFTP host, cloud storage).
6) Policies, training, and off-boarding
Write a file-sharing policy, train staff, and promptly revoke access for departing employees. OCR audits check for these basics.
Channels Compared: What to Use—and When
Secure Portal (Best default)
- What it is: A cloud platform with user accounts, MFA, role-based access, and encrypted file sharing PHI protections.
- Pros: Centralized HIPAA audit logs, granular permissions, version control, big-file support (CBCT), easy revocation.
- Cons: Requires account setup and user hygiene (passwords, MFA).
- BAA: Required with the portal vendor.
SFTP/Managed File Transfer
- What it is: Secure file transfer healthcare via SSH/TLS with admin-controlled credentials.
- Pros: Very secure, great for bulk and automated transfers; pairs well with practice management systems.
- Cons: More IT setup and user friction; still needs audit and retention strategy.
- BAA: Required with host/provider.
HIPAA Compliant Email
- What it is: Email platform with enforced encryption and compliance features.
- Pros: Ubiquitous, straightforward, good for simple correspondence and small attachments.
- Cons: Not ideal for very large files; versioning and access revocation are weaker than portals.
- BAA: Required with email vendor; make sure encryption is automatic, not user-optional. Paubox
Bottom line: Use a portal (or SFTP) as your primary channel; reserve HIPAA compliant email for light correspondence or when the portal is unavailable.
Building a HIPAA-Safe Workflow With Your Lab
Step-by-Step for a Portal-First Workflow
- Set roles and MFA. Give each staff member a unique login; MFA required. Remove shared logins.
- Upload efficiently. Name files consistently:
LASTNAME_FIRSTNAME_DOB_Tooth_ScanType_Date. - Attach only what’s needed. Rx, scans (STL/PLY), shade photos, bite records, and case notes.
- Tag the lab case. Tooth numbers, material preferences, due date, and delivery address.
- Share to the lab team. Grant least-privilege access; revoke once the case is complete.
- Document everything. The system should log access, downloads, and comments for HIPAA audit logs.
- Archive securely. Apply retention rules that meet HIPAA documentation expectations (often ≥6 years) and your state requirements.
If You Must Use Email
- Use a HIPAA compliant email provider that automatically encrypts outgoing PHI.
- Put PHI in a secure attachment (not the subject line); avoid PHI in unencrypted bodies.
- Use time-limited secure links (if supported) and require recipient authentication.
- Share passwords through a separate channel (text/voice) when sending encrypted archives.
- Keep the case small: Rx, a few photos—send large scans through the portal later. Paubox
Practical Examples You Can Copy Tomorrow
Example 1: Single Crown (Digital Files)
- You send: Rx, prep/opp STL files, buccal bite, 2 shade photos.
- Channel: Portal with MFA and logging.
- Associated Dental Lab tip: Include due date and material (zirconia vs. e.max) in the case notes to streamline design and reduce clarifying calls.
Example 2: Implant Crown With CBCT
- You send: DICOM/CBCT via portal (or SFTP for very large files), scan body photos, STL models, Rx.
- Security: Encrypted upload + multifactor login; confirm lab receipt in-portal (creates an audit trail entry).
Example 3: Complete Denture Records
- You send: PVS impression photos, jaw relation records, shade, and patient smile photos.
- Channel: Portal to handle large image sets; local pickup for physical impressions if you’re in Los Angeles.
Example 4: Rush Repair
- You send: Case photos and Rx via portal; arrange local pickup (LA area).
- Why it works: Speed plus security—digital triage first, then physical logistics.
Policy Must-Haves: Your File-Sharing Playbook
Access & Identity
- Unique accounts only; multi-factor authentication portal required.
- Immediate off-boarding for role changes or departures.
Encryption
- Data encrypted at rest and in transit across all systems.
- Avoid consumer cloud tools unless they offer HIPAA features and a BAA.
Audit & Retention
- Enable detailed HIPAA audit logs; review them regularly.
- Retain logs and relevant documentation for at least six years (or longer if state law requires). Compliancy Group
Vendor Management
- Maintain an inventory of every system that touches PHI; keep current BAAs on file.
- Reassess vendors annually (security, uptime, breach history).
Common Pitfalls—and How to Avoid Them
- Free file-drop links with no BAA. If a cloud vendor won’t sign a BAA, don’t use it for PHI.
- Emailing PHI from personal accounts. Only send PHI through HIPAA compliant email configured for encryption. Paubox
- No MFA on portals. Today’s threat climate makes MFA essential and likely to be mandated.
- Undefined retention. If you can’t find an access log six months later, you’re exposed in an OCR inquiry. Keep logs and policies organized.
- Oversharing PHI. Stick to the minimum necessary. Scrub screenshots and crop photos to remove extraneous identifiers.
How Associated Dental Lab Fits In
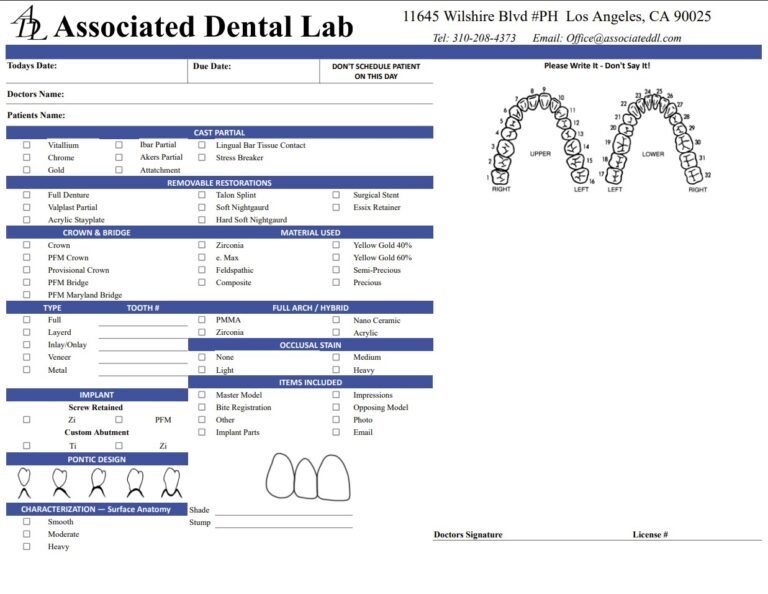
- Simple case intake. Use our lab slip and send models, impressions, or digital files—including local pickup options for Los Angeles practices.
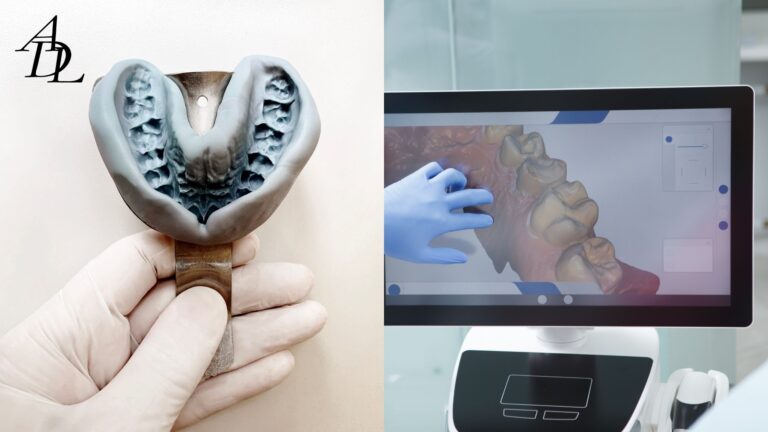
- Quality first. All restorations are fabricated in our Los Angeles lab under strict quality control and regulatory compliance—supporting your clinical and compliance goals.
- Digital or analog—your choice. We work from secure digital submissions or physical impressions and collaborate closely to reduce questions, reworks, and delays.
A 12-Point Checklist for HIPAA Compliant File Sharing Dental Teams
- Inventory all systems that store/transfer PHI (portal, email, cloud, SFTP).
- Execute BAAs with each applicable vendor.
- Enforce MFA and unique logins for every user.
- Enable encryption at rest and in transit across platforms.
- Create a naming convention that contains only necessary identifiers.
- Standardize what to send per case type (Rx, scans, photos, bite).
- Use portal-based messaging to keep HIPAA audit logs in one place.
- Avoid consumer cloud links without BAAs.
- Train staff; document annually.
- Off-board access instantly when roles change.
- Review logs monthly; keep for ≥6 years.
- Test incident response (lost device, wrong recipient) and document outcomes.
Frequently Asked Questions (FAQ)
1) Is regular email allowed for HIPAA compliant file sharing?
Yes—if you use a HIPAA compliant email provider that automatically encrypts messages containing PHI and you have a BAA with that vendor. For larger files or better access control, a multi-factor authentication portal is safer.
2) Do I need a HIPAA BAA with my dental lab?
When sharing PHI for treatment, dental labs are considered health care providers; a BAA with the lab is generally not required for that use case. However, you do need BAAs with any third-party vendors (email, portal, cloud storage) that create, receive, or transmit PHI for your practice.
3) What should my audit logs capture?
Good HIPAA audit logs track who accessed, viewed, downloaded, or shared PHI; timestamps; IP/location; and admin changes. OCR evaluates your documentation in audits, and many programs retain logs for at least six years.
4) Is encryption mandatory?
Encryption is an “addressable” safeguard under the Security Rule—meaning it’s expected unless a documented risk analysis justifies an alternative. Proposed updates would strengthen expectations around encryption and MFA, and OCR already promotes MFA as best practice.
5) How should I send CBCT/DICOM files?
Use your secure portal or SFTP (best for large files). Avoid standard email for very large datasets. Keep the secure file transfer healthcare channel encrypted and logged, and share only the minimum necessary images.
6) How do I verify my vendor is HIPAA-ready?
Confirm encryption, MFA support, audit logging, data retention options, and incident reporting. Most importantly, obtain a signed HIPAA BAA from the vendor. HHS.gov
7) Can patients request unencrypted communication?
If a patient insists on unencrypted email after informed warning of the risks, document their request and limit PHI to the minimum necessary. Nonetheless, your default should remain HIPAA compliant file sharing via secure channels.
Conclusion
Digital dentistry thrives on fast, precise collaboration—and that includes the secure movement of PHI. Choosing a portal-first workflow with robust encryption, multi-factor authentication, HIPAA audit logs, and proper HIPAA BAA coverage puts your practice on solid footing. Use HIPAA compliant file sharing dental practices for every case—crowns, implants, dentures, and more—and you’ll protect patients, minimize risk, and streamline communication with your lab.
About Associated Dental Lab
Associated Dental Lab supports both secure digital submissions and traditional impressions, with local pickup and strict quality control from our Los Angeles facility. When you need a partner that respects privacy as much as precision, contact Associated Dental Lab—a dentists’ trusted Full-Service Dental Lab—to set up a HIPAA-safe, frictionless file-sharing workflow tailored to your team. Associated Dental Lab
Ready to modernize your case submissions? Send your next case with confidence—fast, secure, and compliant.